🏛️ Code Review Council¶
AI reviews AI-generated code. Evidence required. Every blocker must prove itself.
⚡ How It Works¶
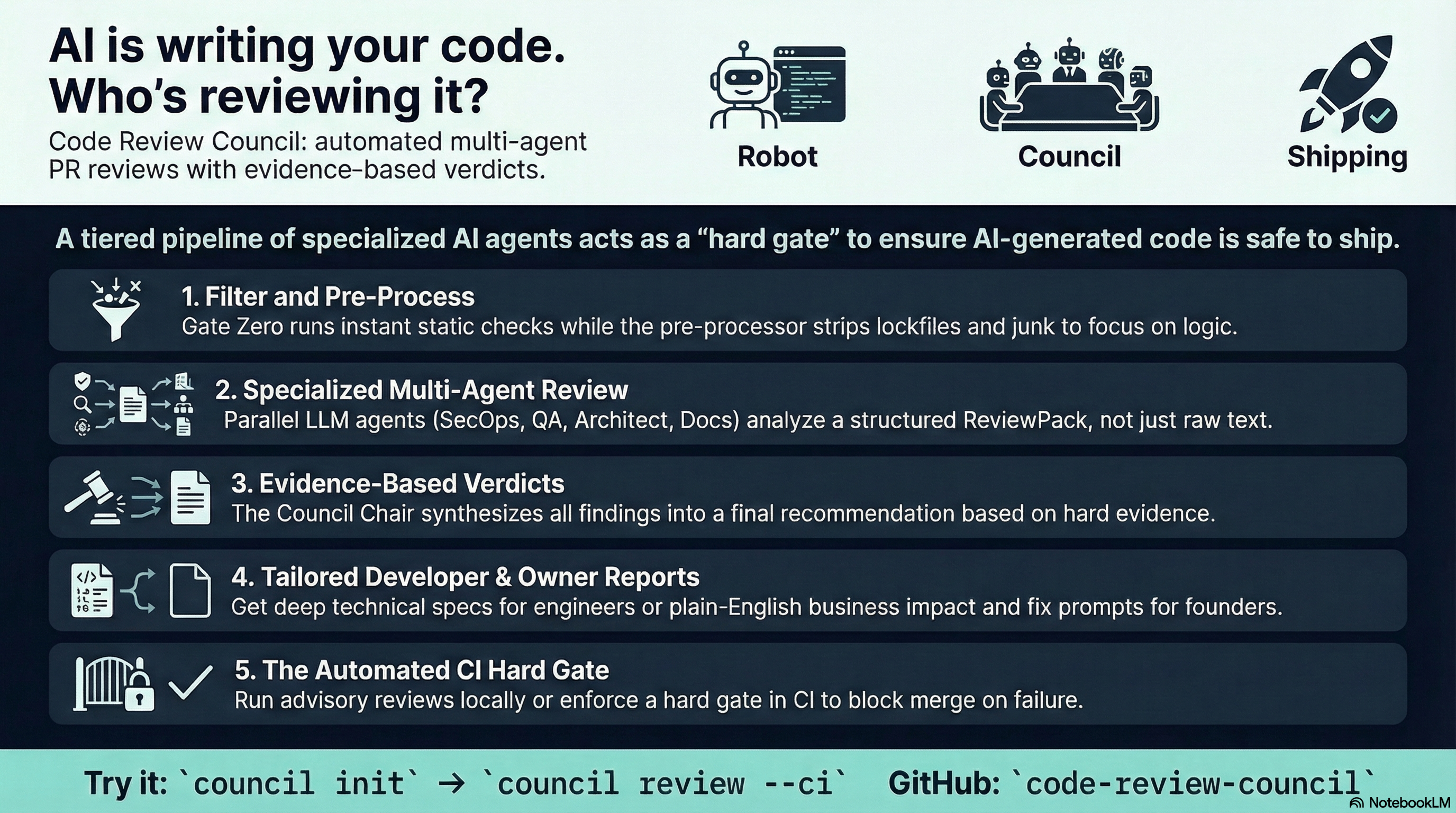
Every PR passes through a five-stage pipeline — deterministic checks first, LLM analysis only where it adds value:
| Stage | Name | What Happens | Cost |
|---|---|---|---|
| 0 | 🔒 Gate Zero | Secrets, lint, types, missing docs — under 2 seconds | Zero |
| 1 | ✂️ Diff Preprocessor | Filters lockfiles and generated code, enforces token budgets | Zero |
| 2 | 📦 ReviewPack | Builds structured context: symbols, test map, policy violations | Zero |
| 3 | 🤖 Reviewer Panel | SecOps, QA, Architect, Docs — parallel, evidence required | 4× LLM |
| 4 | 🪑 Council Chair | Synthesises findings, requires exploit chain for blockers, renders verdict | 1× LLM |
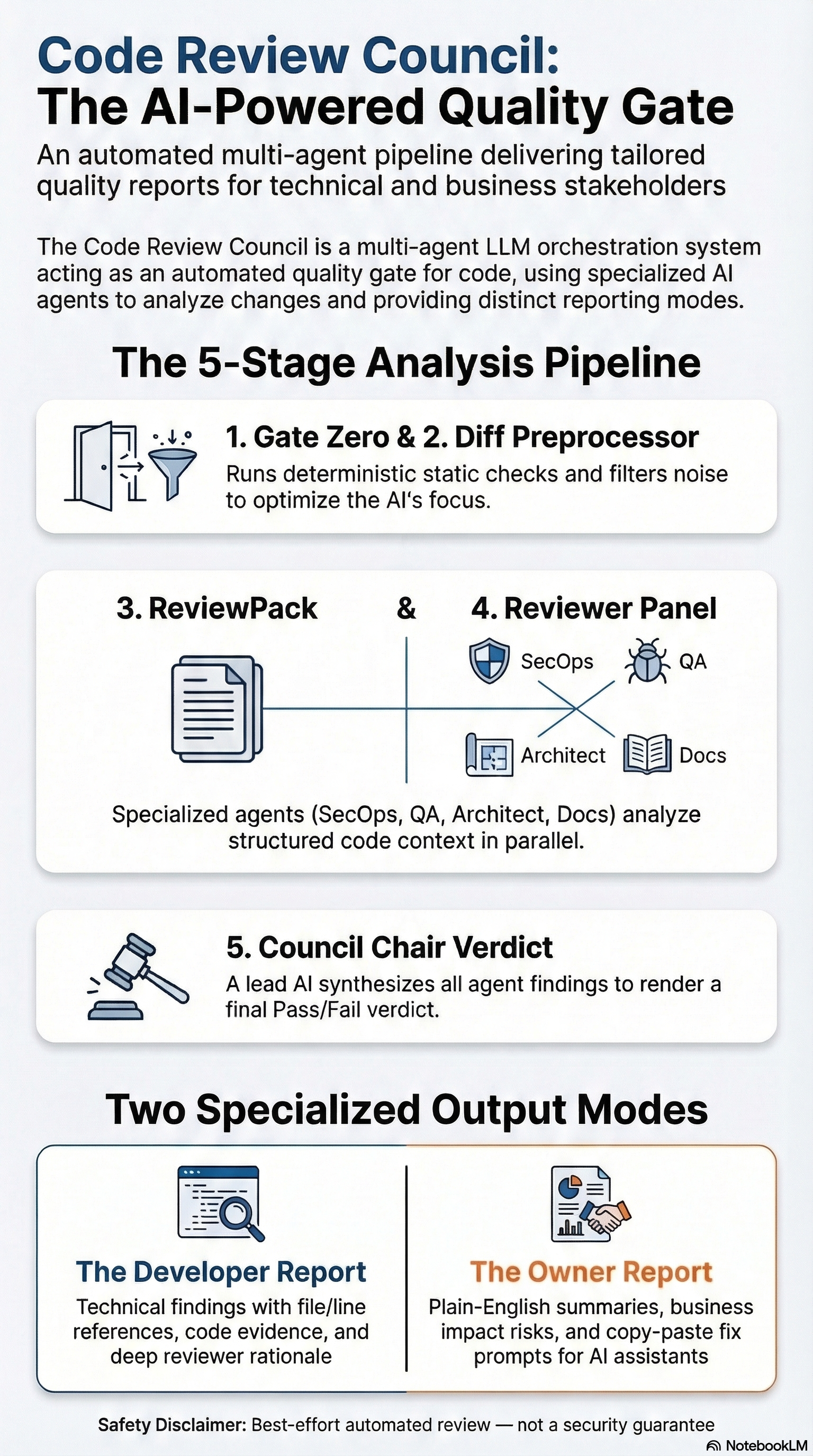
🎯 Two Outputs, One Review Engine¶
| 🧑💻 Developer | 🧑💼 Owner | |
|---|---|---|
| Audience | Engineers | Product / Leadership |
| Focus | File/line findings, evidence, fix suggestions | Plain-English risk, ship/no-ship recommendation |
| Extra | Policy references, Chair rationale | Copy-paste fix prompt for AI coding agent |
| Review strength | Full | Full — same engine, different presentation |
📊 Real Verdict¶
This is actual output from Council reviewing its own PR:
Overall verdict: PASS (confidence: 0.90)
secops PASS 0 findings
qa PASS 2 findings (2 warnings accepted)
architect PASS 0 findings
docs PASS 0 findings
Runtime: 48 seconds
→ See the full breakdown on the Self Review page.
⚡ Try It Locally¶
git clone https://github.com/vishal8shah/code-review-council
cd code-review-council
pip install .
council init
export GOOGLE_API_KEY=...
council doctor --branch main
council review --branch main
Quality gate, not a guarantee
Council is not a substitute for human engineering judgment. LLM findings are evidence-backed but not infallible — hallucination risk is reduced by design (structured context, mandatory file/line references, exploit chain requirements) but not eliminated. Cost and latency vary by model and diff size. Use restricted BYOK keys on repos you control.
🗺️ Explore the Docs¶
| Page | What You'll Find |
|---|---|
| Overview | Why this exists, the multi-LLM approach, the autonomous loop vision |
| Getting Started | Install, init, first review, CI setup |
| Design | Architecture decisions, ReviewPack, evidence-based Chair |
| Security | BYOK model, key scoping, threat mitigations, merge gates |
| Workflows | PR workflow vs BYOK workflow, artifact locations |
| Self Review | Council reviewing its own PR — real output, 26 fixes, 286 collected tests |
| FAQ | Fork PRs, model config, cost tuning, PR comments |
| Contributing | Setup, tests, adding a new reviewer persona |